Wpa2 Infostrada Wifi
The difference between WEP, WPA and WPA2 WiFi security algorithms have been through many changes and upgrades since the 1990s to become more secure and effective. Different types of wireless security protocols were developed for home wireless networks protection. The wireless security protocols are WEP, WPA, and WPA2, serving the same purpose but being different at the same time. Not only do the protocols prevent unwanted parties from connecting to your wireless network, but also wireless security protocols encrypt your private data sent over the airwaves. No matter how protected and encrypted, wireless networks cannot keep up in safety with wired networks. The latter, at their most basic level, transmit data between two points, A and B, connected by a network cable.
To send data from A to B, wireless networks broadcast it within their range in every direction to every connected device that happens to be listening. Let's have a closer look at WEP, WPA, and WPA2 wireless security protocols. Wired Equivalent Privacy (WEP) WEP was developed for wireless networks and approved as a Wi-Fi security standard in September, 1999. WEP was aimed to offer the same security level as wired networks, however there are a bunch of well-known security issues in WEP, which is also easy to break and hard to configure. Despite all the work that has been done to improve the WEP system it still is a highly vulnerable solution. Systems that rely on this protocol should be either upgraded or replaced in case security upgrade is not possible. WEP was officially abandoned by the Wi-Fi Alliance in 2004.

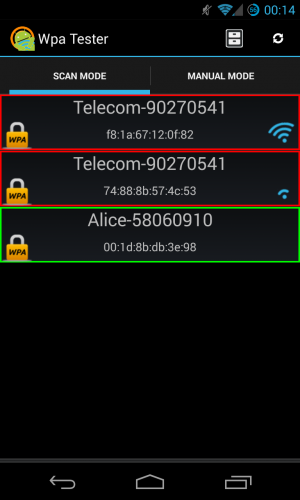
Infostrada Wifi Wpa Calculator ->>>DOWNLOAD (Mirror #1) wpa free download - WPA, WEP and WPA keygenerator, WPA on the Move, and. Even if you know you need to secure your Wi-Fi network (and have already done so), you probably find all the security protocol acronyms a little bit puzzling. Repair Winrar Files more.
Wi-Fi Protected Access (WPA) For the time the 802.11i wireless security standard was in development, WPA was used as a temporary security enhancement for WEP. One year before WEP was officially abandoned, WPA was formally adopted.
Most modern WPA applications use a preshared key (PSK), most often referred to as WPA Personal, and the Temporal Key Integrity Protocol or TKIP (/tiːˈkɪp/) for encryption. WPA Enterprise uses an authentication server for keys and certificates generation. WPA was a significant enhancement over WEP, but as the core components were made so they could be rolled out through firmware upgrades on WEP-enabled devices, they still relied onto exploited elements. WPA, just like WEP, after being put through proof-of-concept and applied public demonstrations turned out to be pretty vulnerable to intrusion.
The attacks that posed the most threat to the protocol were however not the direct ones, but those that were made on Wi-Fi Protected Setup (WPS) - auxilliary system developed to simplify the linking of devices to modern access points. Wi-Fi Protected Access version 2 (WPA2) The 802.11i wireless security standard based protocol was introduced in 2004. The most important improvement of WPA2 over WPA was the usage of the Advanced Encryption Standard (AES) for encryption. AES is approved by the U.S. Government for encrypting the information classified as top secret, so it must be good enough to protect home networks.
At this time the main system is when the attacker already has access to a secured WiFi network and can gain access to certain keys to perform an attack on other devices on the network. This being said, the security suggestions for the known WPA2 vulnerabilities are mostly significant to the networks of enterprise levels, and not really relevant for small home networks. Unfortunately, the possibility of attacks via the Wi-Fi Protected Setup (WPS), is still high in the current WPA2-capable access points, which is the issue with WPA too. And even though breaking into a WPA/WPA2 secured network through this hole will take anywhere around 2 to 14 hours it is still a real security issue and WPS should be disabled and it would be good if the access point firmware could be reset to a distribution not supporting WPS to entirely exclude this attack vector. Which security method will work for your network Here is the basic rating from best to worst of the modern methods available on modern (after 2006) routers: • WPA2 + AES • WPA + AES • WPA + TKIP/AES (TKIP is there as a fallback method) • WPA + TKIP • WEP • Open Network (no security at all) The best way to go is deactivate Wi-Fi Protected Setup (WPS) and set the router to WPA2 +AES. Access Invoice Database. And as you go down the list, the less secure your network is going to get.